Researchers Hack 3D Printer to Sabotage a Drone
Posted on October 25, 2016 by Keith Lynn
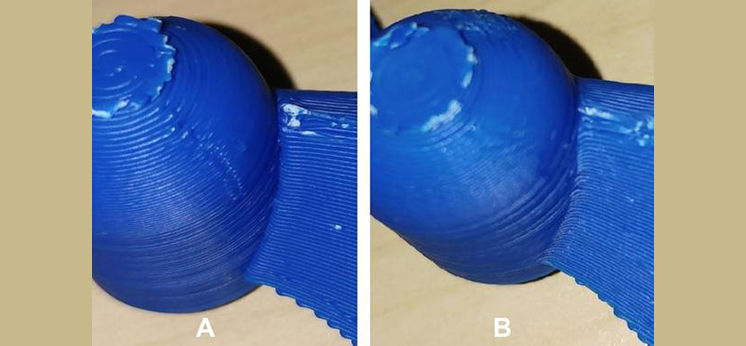
SoC faculty member Mark Yampolskiy is part of a team of researchers from three universities (University of South Alabama, Ben-Gurion University, and Singapore University of Technology and Design) who have combined their expertise to prove the existence of yet another Pandora’s box of computerization: the security of Additive Manufacturing (a.k.a. 3D Printing). In a recent paper titled “dr0wned,” they have shown how to sabotage the quality of a 3D printed functional part, leading to the destruction of the device. In their experimental proof of concept, viewable on Youtube [https://youtu.be/zUnSpT6jSys], they destroyed a $1000 drone by hacking into the computer used to control the 3D printing of replacement propellers. After hacking into the computer, the researchers identified the blueprint file of the propeller and inserted defects that could not be detected by a visual inspection. During flight tests, the sabotaged propeller broke apart while the drone was rising. The consequences: the drone fell from the sky, smashed on the ground, and was irreparably damaged.
While this particular attack only destroyed $1000 of equipment, similar attacks can reach a much larger scale. According to the Wohlers Report, a renowned annual survey of advances in Additive Manufacturing, the AM industry accounted for $5.165 billion of revenue in 2015. Further, 32.5% of all AM-generated objects are used as functional parts. At the time of writing, the 3D Printing Business Directory [http://www.3dprintingbusiness.directory/] lists 117 different industries that employ AM, including aerospace, automotive, and defense. Let’s scale up: imagine that an adversary can sabotage functional parts employed in an airplane’s jet engines. Such an attack could cost lives, lead to economic loss, disrupt industries relying on AM, and threaten the country’s national security. These consequences and the ever-growing revenue of the AM industry will attract the attention of many adversaries, ranging from criminals to state actors, who will aim either for profit or for geopolitical power.
It should be noted that “dr0wned” is not the first article that raises the issue. However, all prior research has focused on a single aspect of a possible attack, assuming that all other attack elements are feasible. The “dr0wned” article leaves no room for speculation. It provides scientifically sound evidence of such an attack. It presents a methodical approach to preparing and effecting the attack: how options can be identified, how the difficulty of attack options can be estimated, and how the effects of possible manipulations can be evaluated. In combination with the pervasiveness and importance of AM, this article underlines the need to face yet another battlefield on the security front – the Security of Additive Manufacturing.
-

Scholarship and Awards Luncheon
The School of Computing celebrated excellence and achievement during i...
May 14, 2026 -

SoC hosted an industry discussion of successful alumni to help students navigate the transition into the workforce
SoC hosted an industry discussion of successful alumni to help student...
March 27, 2026 -
SoC Students Complete Impactful Internships with USA's CSC Networking Team
SoC Students Complete Impactful Internships with USA's CSC Networ...
December 16, 2025 -

Alumnus Jay Maru Inspires Seniors to Lead in an AI-Powered Future
The School of Computing recently welcomed alumnus Jay Maru, founder of...
October 7, 2025
