The Vulnerability of 3D Printing
Posted on November 2, 2018
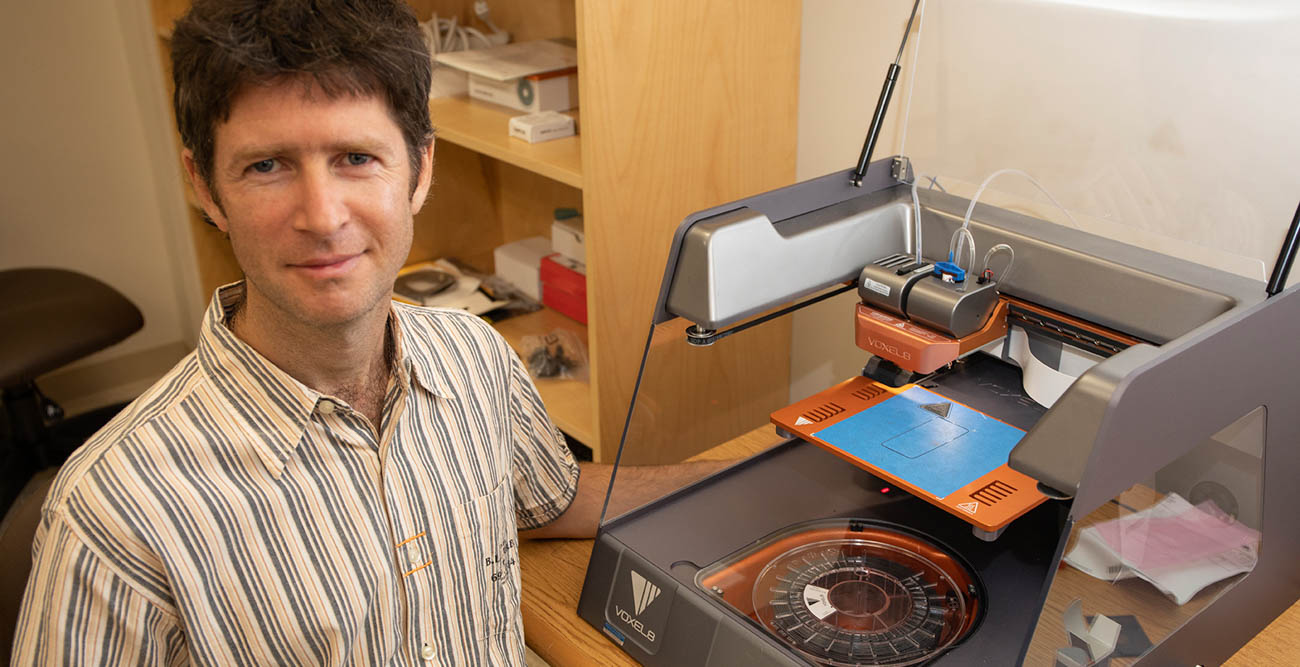
Dr. Mark Yampolskiy, assistant professor in the School of Computing at the University of South Alabama, is gaining international attention for his research into the security of 3D printing, arguing that protection is a necessity for the growing technology.
Yampolskiy has been cited in several publications, most recently by “Innovation Toronto,” on the growing need for 3D printer security. That story referred to a 2016 experiment carried out by Yampolskiy and fellow researchers from Israel and Singapore, who hacked into a desktop computer and altered a design file for a quadcopter drone propeller. Later, the drone propeller, which was made using a 3D printer, broke during flight and caused the drone to crash.
“Our purpose was to demonstrate how people can attack manufacturing systems, and what harm it can cause. Plus, we wanted to show companies and others scientists that the security of 3D printers is a rapidly emerging problem. This was the first realistic instance of such an attack demonstrated in the research literature,” Yampolskiy said. “To find ways to protect manufacturing systems, it was necessary to understand first how such systems can be attacked.”
The use of 3D printing technology has grown rapidly into a $6 billion industry, printing everything from customized models and functional parts of jet engines to prosthetic devices and tools for the International Space Station. Unfortunately, experience has shown that hackers can usually get into even the most protected of networks.
“In the U.S., about 16 percent of manufacturing companies already employ 3D printing, and another 16 percent are planning to use it in the near future,” Yampolskiy said. “Further, the military is investigating thoroughly its integration into their logistics, to simplify and speed up supplying of replacement parts on demand.”
Yampolskiy, who joined South’s faculty in 2014, is continuing to work with his collaboration partners on solutions that would enable detection of sabotage attacks. For example, partnering with his collaborators from Israel, he is developing solutions based on so-called “side-channels,” such as acoustic emanations or power consumption of a 3D printer. Side-channels of a verifiable benign process can be recorded and transformed to a master signature of a 3D printing process.
According to Yampolskiy, if the same object has to be manufactured again, its side-channel-based signature can be computed and compared with the master signature. Significant difference between both signatures would indicate a potential sabotage attack. This knowledge would prevent such a part from being integrated into a real system, and consequently avoid a potential disaster.